Trends
GreyNoise Trends
What is GreyNoise Trends?
The GreyNoise Trends feature takes the lens that GreyNoise uses to view internet-wide scanning and focuses on the exploit, activity, or tool associated with a GreyNoise Tag.
GreyNoise Tags are essentially a signature-based detection method. Tags cover five primary categories: Activity, Tool, Actor, Search Engine, or Worm. Think of tags like network signatures, but with additional context such as tag intent, category, and related CVEs. GreyNoise continues to add tags to cover activities such as new vulnerabilities or CVEs, updates to scan or crawl behaviors, or releases of malicious tools.
The GreyNoise Trends feature allows a user to view GreyNoise data as it relates to a specific tag. The GreyNoise Trends page for a specific tag can be reached by clicking a tag name on an IP Details page or the Tags library.
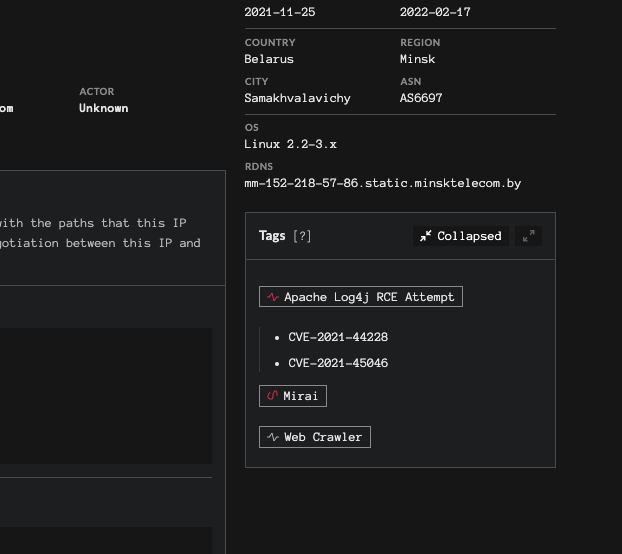
Navigation from IP Details Page
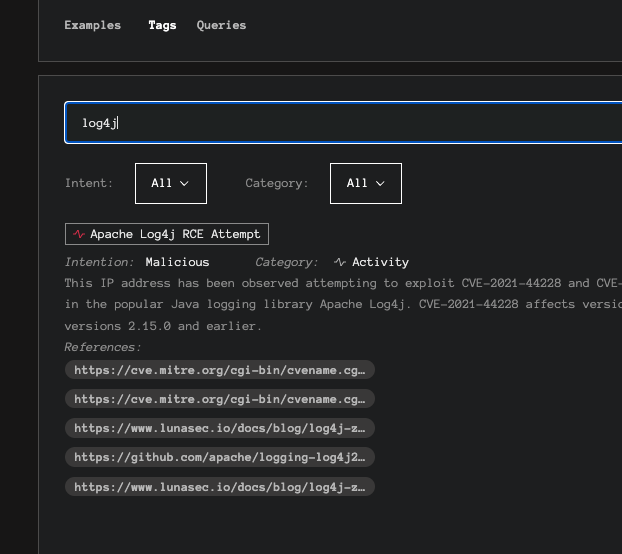
Navigation from Tags Library
The GreyNoise Trends page for a Tag is broken up into a few different sections. The topmost section includes:
- Tag Name - This is the name that GreyNoise has assigned for this signature
- Tag Metadata - This includes the tag intent (benign, unknown, or malicious), the Tag Category, and a short description of the tag
- Related CVEs - If applicable, the CVEs associated with the tag
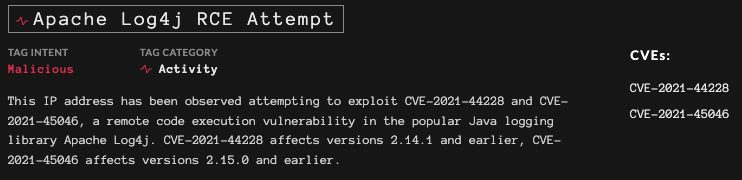
Tag Metadata Section
Below the metadata section, a trends graph and timeline are included:
- The trends graph shows a 3, 10, or 30 day graph of the unique IPs scanning for this activity. If hovered over, the unique IP counts are shown for each data point.
- The timeline includes the sequence of recorded events that GreyNoise has identify as associated with this activity.

Graph and Timeline Section
Along the right-hand side of the tag, four additional sections are provided:
View tagged IPs
- View tagged IPs: This link navigates to the GNQL results for the tag
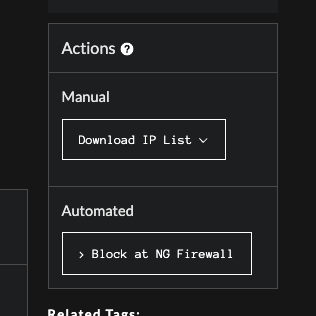
Actions
- Actions: Provides the ability to access IP lists associated with this tag for two use cases
- For Manual Usage: Download a list of IPs in JSON, CSV or TXT format
- For Automated Usage: Get a dynamically updated URL to use in firewall blocking
Block List Change Notice06.15.22 | At the initial launch of this feature, the Block List URLs did not require authentication to use. As this feature is now out of BETA, an authorization mechanism will be put in place to use this feature and will require updates to existing usage of the URLs. We intend to make this transition as frictionless as possible and continue to offer the capability to our Community users. Please see the next page for information on how to Block with GreyNoise Trends.
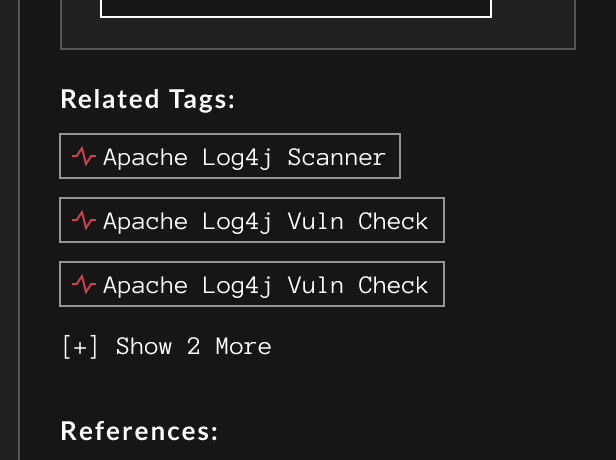
Related Tags
- Related Tags: Provides a list of other GreyNoise Tags that are related to the current tag. This is often useful when tags exist for different levels of an exploit, such as a vuln check versus an actual exploit attempt.
References
- References: Provides a list of external references used to generate the signatures for this tag.
Updated 2 months ago
