Tag Trends - Anomalies
Tag Trends - Anomalies
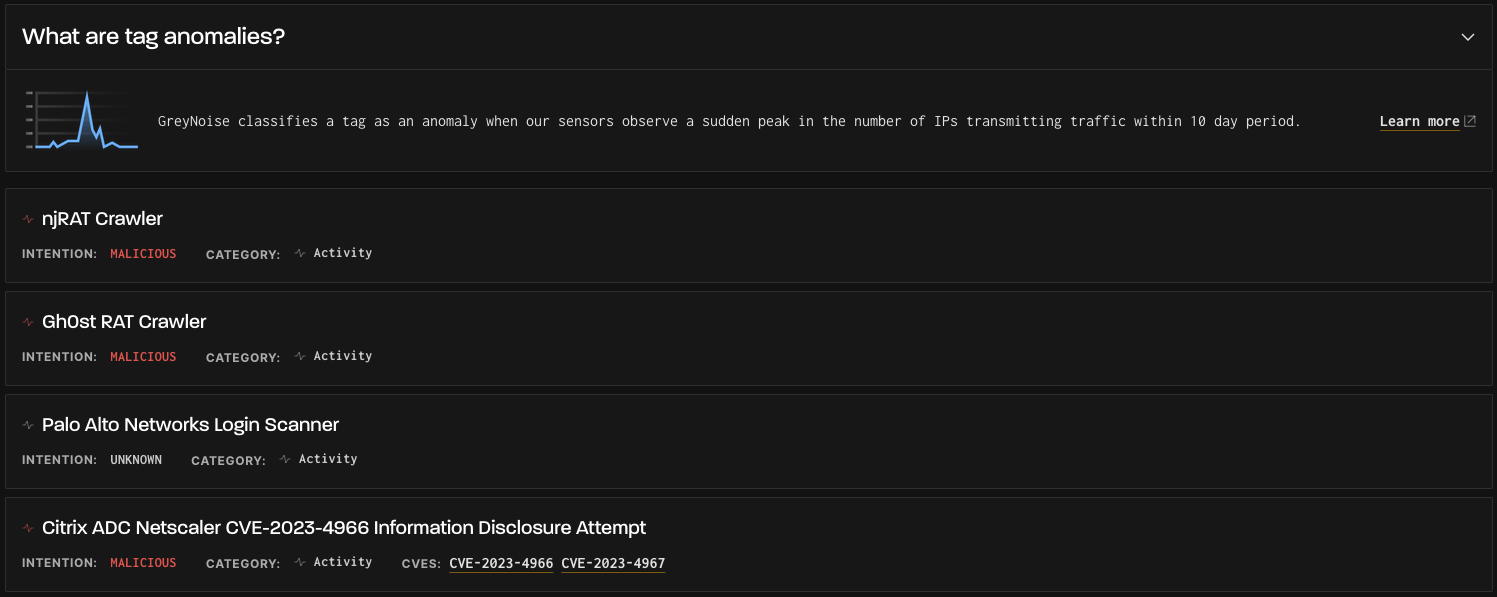
What are tag anomalies? - GreyNoise classifies a tag as an anomaly when our sensors observe a sudden peak in the number of IPs transmitting traffic within a 10-day period. The list is sorted in descending order based on the size of the anomaly and displays the top ten tags.
Each tag card in the list contains the following:
- Tag Name
- Tag Category
- Tag Intent (Benign, Unknown, or Malicious)
- Associated CVEs
Tag Trends - Anomalies Tab
How Anomalies Detection Works
Detecting trends and anomalies is about finding deviation from previous behavior, particularly in a positive direction.
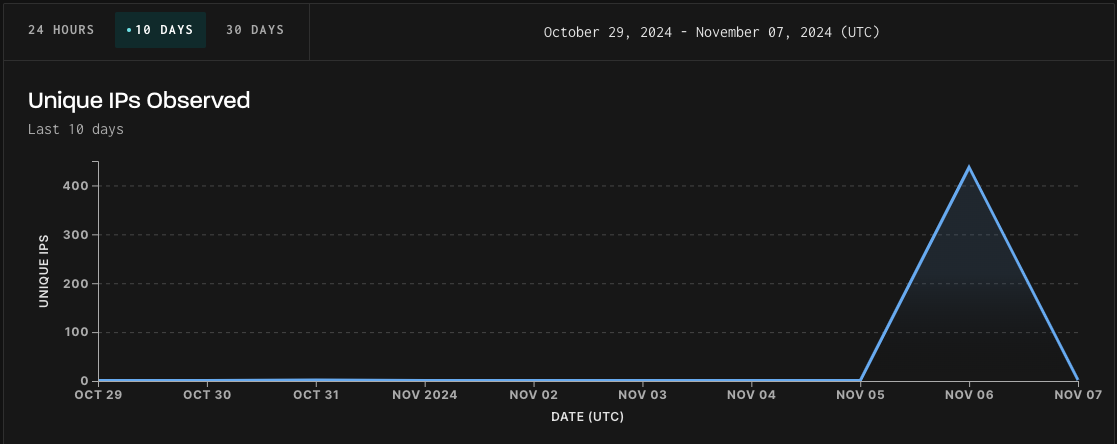
To detect an anomaly, we use a moving window to determine which sample(s) have the largest (positive) deviation from the average value for that window. The peak values are then subjected to the percent change formula so that we can compare anomalies and trends for each tag:
(Peak Height - long term avg.)/long term avg.
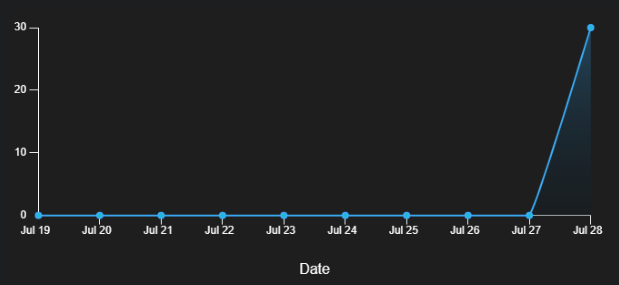
Ranking the output of these algorithms, we present the tags with the largest recent increase in trend and the tallest recent peak, both relative to previous average behavior.
What do I do with Anomalies Tags?
- Verify peaks in an activity that may have appeared as groupings of alerts in a SIEM or logging platform.
- Find out if you're the only one observing erratic scanning or exploitation activity or if it's happening worldwide.
- Determine what days a benign scanner does its scanning
- Show historical scanning behaviors
Updated about 2 months ago
